|
|
During a Domain Controller (DC) promotion, administrators create a Directory Services Restore Mode (DSRM) local administrator account with a password that rarely changes. The DSRM account is an “Administrator” account that logs in with the DSRM mode when the server is booting up to restore AD backups or recover the server from a failure.
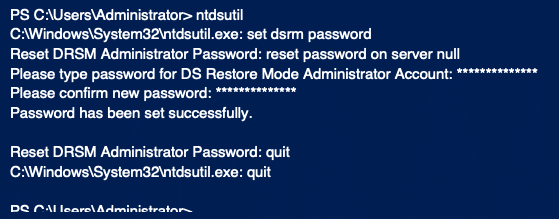
Attackers could abuse DSRM account to maintain their persistence and access to the organization’s Active Directory. Administrators set the DSRM password while configuring Active Directory and typically do not follow the recommendation of changing its passwords regularly. Knowing this, attackers will attempt to create a permanent backdoor to establish a connection in the future. An attacker can change the DSRM account password by running the following command on every DC (or remotely against every DC by replacing “null” with DC name).
Once an attacker has the DSRM password, it is possible to use this account to log on to the DC over the network as a local administrator. An attacker can extract both the local administrator and AD administrator password hashes using an open-source credential dumping tool, such as running Mimikatz with the commands “lsadump::sam” and “lsadump::lsa /patch”, respectively.
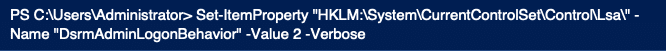
With the local administrator password hash, the attacker can change the Windows registry to log into the DC using DSRM hashes without rebooting the server. The attacker can confirm the “DsrmAdminLogonBehavior” registry key value under HKLMSystemCurrentControlSetControlLsa and create possible REG_DWORD values as shown below:
- 0 – the default value. Can use the DSRM administrator account only if the DC starts in DSRM.
- 1 – Use the DSRM administrator account to log on if the local AD DS service is stopped.
- 2 – Always use the DSRM administrator account (This setting is not recommended because password policies do not apply to the DSRM administrator account).
The attacker will try to set the registry key “DsrmAdminLogonBehavior” value to 2, as shown below.
An attacker further uses additional techniques such as Pass the Ticket (PTT) to access the DC and laterally move on the network. The following Mimikatz commands help to achieve their goals.
- “privilege::debug”
- “sekurlsa::pth /domain:attivo1.local /user:Administrator /ntlm: fc063a56bf43cb54e57a2522d4d48678”
How to Mitigate DSRM Account Misconfigurations?
Security administrators must ensure the DSRM account passwords are unique for every Domain Controller and change them regularly (at least as often as other account passwords). Also, ensure the registry key DsrmAdminLogonBehavior is not set to 2, and the same registry key value does not exist by default.
Conclusion
The DSRM account activation provides a useful attack method to pull domain credentials and maintain persistence across the organization’s network. Administrators should implement appropriate password and registry key settings for these accounts and continuously monitor for misconfigurations that expose Active Directory to an attack.
Singularity™ Ranger AD is a cloud-delivered solution designed to uncover vulnerabilities in Active Directory and Azure AD. Get additional AD attack detection and conditional access capabilities to protect enterprise identity infrastructure with Singularity Ranger AD Protect.



